Who ever thinking like this. To protect yourself is concern and do something that is safety for you. Take care!
The information about client of Sony PlayStation Network leaks.
(CNN) -- It's been seven days since Louis Pietig's PlayStation gaming system worked -- and he's pretty mad about that.
But far more infuriating, he said, is the fact that Sony kept him in the dark for so long about the reason for an ongoing PlayStation Network outage: a hack of its online system that compromised users' personal data possibly including credit card information.
On that subject, Pietig is furious.
"It's ridiculous, the transfer of information from Sony to the end game users," he said by phone, after responding to a query from the @cnntech Twitter feed. "It's deplorable that they wouldn't tell us that you should look at your credit card."
Pietig, a 25-year-old in New York, said he already cancelled the credit card he linked with Sony's network because he was concerned about the security of his financial information.
"If you think for a second that someone may have seen your credit card and you don't get a new one, you're an idiot," he said...read more from source
More Infomation here
Thursday, 28 April 2011
Wednesday, 6 April 2011
M&S customers hit by Epsilon e-mail hack
Read article from BBC News http://www.bbc.co.uk/news/technology-12983177
Labels:
email hack bbc news
Saturday, 2 April 2011
Tuesday, 1 March 2011
Google Chrome patched 19 vulnerabilities
After Google said to paying $20000 for anyone can hack Google Chrome.
Computerworld said "Google on Monday patched 19 vulnerabilities in Chrome, paying nine researchers $14,000 in bug bounties for reporting the flaws."
Computerworld said "Google on Monday patched 19 vulnerabilities in Chrome, paying nine researchers $14,000 in bug bounties for reporting the flaws."
Labels:
google chrome hack patched
Thursday, 10 February 2011
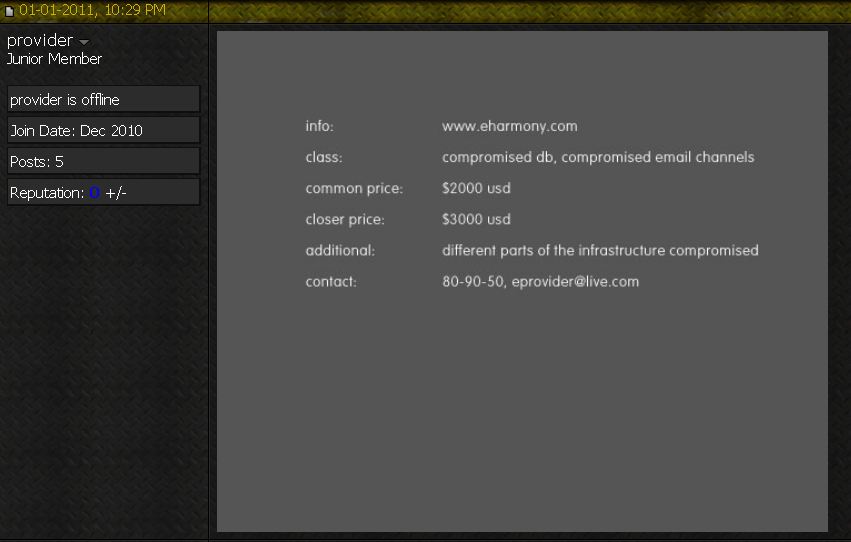
The world of hacking age has many attacks for money
The world of hacking age has many attacks for money. Many hackers both black and white hat want to have the money. They hack into many big business and sell information or blackmail them. According to online dating giant eHarmony was compromised their database and email channels by malicious hacker.
The hacker was post and asks to sell the information.
Another one of hacking is china hacks big oil computer system.
Many business is move on to Cyberspace even though criminal too.
Be awareness of yourself and keep your eye not far from this.
Relate post:
China-hacks-big-oil
Should-go-on-high-alert
internetNews feed
Credit:: krebsonsecurity.com
The hacker was post and asks to sell the information.
Another one of hacking is china hacks big oil computer system.
Many business is move on to Cyberspace even though criminal too.
Be awareness of yourself and keep your eye not far from this.
Relate post:
China-hacks-big-oil
Should-go-on-high-alert
internetNews feed
Credit:: krebsonsecurity.com
Tuesday, 8 February 2011
Russian hacker avoids jail over $10 million cyber theft
Yevgeny Anikin, 27 year old malicious hacker was the lucky man.
He has avoided prison despite pleading guilty for his part in stealing $10 million from the former Royal Bank of Scotland division Worldpay in 2008
He was given a five-year suspended sentence on Tuesday
Read more:
and source
He has avoided prison despite pleading guilty for his part in stealing $10 million from the former Royal Bank of Scotland division Worldpay in 2008
He was given a five-year suspended sentence on Tuesday
Read more:
and source
Thursday, 3 February 2011
Google's paying $20000 to hack Chrome.
Google's paying $20000 to who first that can hack chrome browser.
But I think that it is not fair for the hacker because
Chrome have too much of gain in the browser market.
However, I like the marketing of Google Company.
It is really cool.
But I think that it is not fair for the hacker because
Chrome have too much of gain in the browser market.
However, I like the marketing of Google Company.
It is really cool.
Labels:
google pay hack chrome
Monday, 31 January 2011
Google Android OS can exploit and make leaks of user data by malicious hacker
Happening again, seriously about browser execute the client side script on now in Gingerbread. Java script that can damage an Android user when clicks on a malicious link in an email or in the browser, and an attacker could then read and upload any files on the phone's SD memory card, including things like online banking information, pictures, and saved voicemails. That has tested and confirmed the bug on a Nexus S Smartphone running Android 2.3 by Xuxian Jiang, a security researcher at NC State University.
However, the attacks are still not getting a root exploit.
Source:
However, the attacks are still not getting a root exploit.
Source:
Tuesday, 25 January 2011
“Let the hacking begin” Zuckerberg’s Facebook Fan Page was hacked
Accounting to TechCrunch
Show the snapshot of Zuckerberg’s Fan Page that post is
“Let the hacking begin: If facebook needs money, instead of going to the banks, why doesn’t Facebook let its users invest in Facebook in a social way? Why not transform Facebook into a ‘social business’ the way Nobel Price winner Muhammad Yunus described it? http://bit.ly/fs6rT3 What do you think? #hackercup2011”
Lesson learn for people and Zuckerberg
Source+Credit:
Show the snapshot of Zuckerberg’s Fan Page that post is
“Let the hacking begin: If facebook needs money, instead of going to the banks, why doesn’t Facebook let its users invest in Facebook in a social way? Why not transform Facebook into a ‘social business’ the way Nobel Price winner Muhammad Yunus described it? http://bit.ly/fs6rT3 What do you think? #hackercup2011”
Lesson learn for people and Zuckerberg
Source+Credit:
Labels:
Zuckerberg facebook hacked fan
Monday, 17 January 2011
Car Theft because high-tech what should we do?
"Car thieves of the future might be able to get into a car and drive away without forced entry and without needing a physical key, according to new research that will be presented at the Network and Distributed System Security Symposium next month in San Diego, California." www.technologyreview.com said
source
source
Labels:
car theft high tech
Monday, 10 January 2011
Sunday, 9 January 2011
Google Bangladesh Site was defaced
Google Bangladesh Site was deface OwN3D by TiGER-M@TE.
But Google responds that Google Bangladesh has not been hacked. Apparently this is actually a Bangladeshi DNS registry issue that caused users going to Google.co.bd and other web addresses to be redirected to to another site. The issue is now resolved but may not clear for awhile because of cache issues.
Read more from Source
But Google responds that Google Bangladesh has not been hacked. Apparently this is actually a Bangladeshi DNS registry issue that caused users going to Google.co.bd and other web addresses to be redirected to to another site. The issue is now resolved but may not clear for awhile because of cache issues.
Read more from Source
Labels:
google defaced bangladesh TiGER
Amazon cloud can help hack WiFi networks hahaha
Thomas Roth, a computer security consultant based in Cologne, Germany, says he can hack into protected networks using specialized software that he has written that runs on Amazon's cloud-based computers. It tests 400,000 potential passwords per second using Amazon's high-speed computers.
source
source
Labels:
amazon help hack WiKi
Wednesday, 5 January 2011
Information Disclosure Vulnerability of DD-WRT
According to You are victim of physical attack.
Now easy possible!
On Monday, December 27th, 2010 has a post of DD-WRT Information Disclosure Vulnerability vedio by devttys0. Attacker can access the information about a DD-WRT router and internal clients. The attacker can accessed directly by an unauthenticated. The post show about how to disclosure DD-WRT. It very easy to use a browser and type in the url then information will display. There is a mitigate by disable httpd of DD-WRT router.
Read more from source 1. and source 2 + video.
Take care for anyone who using DD-WRT router.
Hope it help :)
Now easy possible!
On Monday, December 27th, 2010 has a post of DD-WRT Information Disclosure Vulnerability vedio by devttys0. Attacker can access the information about a DD-WRT router and internal clients. The attacker can accessed directly by an unauthenticated. The post show about how to disclosure DD-WRT. It very easy to use a browser and type in the url then information will display. There is a mitigate by disable httpd of DD-WRT router.
Read more from source 1. and source 2 + video.
Take care for anyone who using DD-WRT router.
Hope it help :)
Tuesday, 4 January 2011
Microsoft Confirms Zero-Day After Exploit. Bad news for MS :O
Computerworld "Microsoft today confirmed an unpatched vulnerability in Windows just hours after a hacking toolkit published an exploit for the bug. A patch is under construction, but Microsoft does not plan to issue an emergency, or "out-of-band," update to fix the flaw. The bug was first discussed Dec. 15 at a South Korean security conference, but got more attention Tuesday when the open-source Metasploit penetration tool posted an exploit module crafted by researcher Joshua Drake. According to Metasploit, successful attacks are capable of compromising victimized PCs, then introducing malware to the machines to pillage them for information or enlist them in a criminal botnet." This is the source
I think it too late.
This is exploit
I think it too late.
This is exploit
Sunday, 2 January 2011
There are some quotes of someone
"There is no security on this earth, There is only opportunity." - General Douglas MacArthur
"Its very Easy to Hack Websites ,it just Take One Shell to Upload." - <=Shak=>
"As a young boy, I was taught in high school that hacking was cool." - Kevin Mitnick
"Social engineering bypasses all technologies, including firewalls." - Kevin Mitnick
The quotes found in some website :)
"Its very Easy to Hack Websites ,it just Take One Shell to Upload." - <=Shak=>
"As a young boy, I was taught in high school that hacking was cool." - Kevin Mitnick
"Social engineering bypasses all technologies, including firewalls." - Kevin Mitnick
The quotes found in some website :)
Labels:
quotes hacker cracker
Hack cellphones, very easy :), just phone number
Today, smartphones including the iPhone, Blackberry, and Android devices comprise about 21% of the cell phone market, and often contain sensitive information like other phone numbers, e-mails, and banking information.
Read more in Source
There are some solution
Read more in Source
There are some solution
American Honda hacked 2.2 million customers' personal data.
Personal data are including e-mail addresses, VINs and login information has been
stolen by unknow hackers.
Day by day hacker are thieves of personal information.
They annoying people.
source ::
stolen by unknow hackers.
Day by day hacker are thieves of personal information.
They annoying people.
source ::
Labels:
honda hacked customer
Subscribe to:
Comments (Atom)